
10
Actions on Objectives

9
AI C&C

8
Persistence
7
Lateral Movement

6
Privilege Escalation
5
Tool & Environment Interaction
4
Reasoning Time Execution
3
Instruction & Weaponization
2
Trust & Manipulation

1
AI Recon
AI systems - particularly LLMs, and agentic workflows - introduce a fundamentally new risk surface to modern software systems. Unlike traditional application vulnerabilities, AI failures frequently arise without exploitation, without malware, and without unauthorized access. Instead, incidents emerge from normal system behavior operating without sufficient control over goals, authority, and memory.
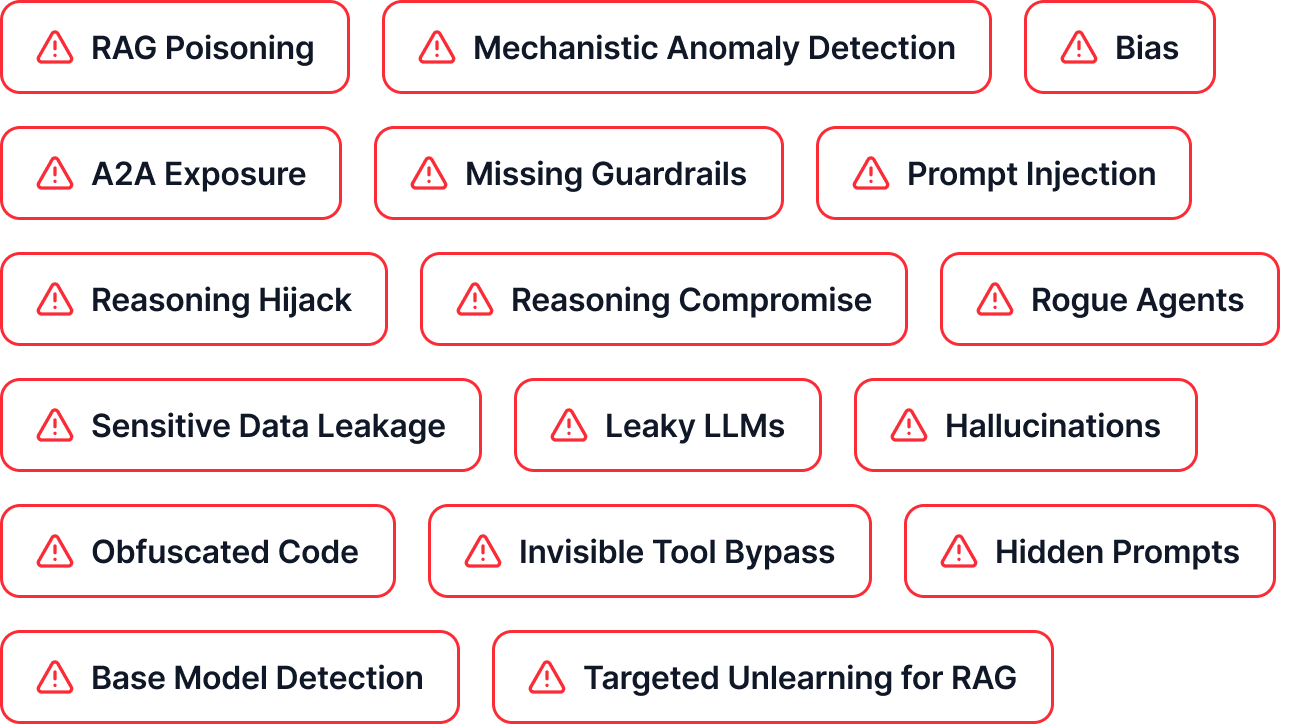
This new landscape requires a new approach - in effect, a new kill chain. One that reframes AI security from the classic approach, and even a “prompt-level” concern, into a system-level governance problem. Because AI systems introduce risks that differ materially from traditional software.

Stage 1
AI Recon
Stage 2
Trust Establishment & Manipulation
Stage 3
Instruction & Input Weaponization
Stage 4
Reasoning & Time Execution
Stage 5
Tool & Environment Exploitation
Stage 6
Privilege Escalation
Stage 7
Lateral Movement
Stage 8
Persistence
Stage 9
AI-Native Command & Control
Stage 10
Actions on Objectives